Real-Time Threat Monitoring Techniques Used by Experts
Cyber security has become more important than ever. In 2026, cyber threats are faster, smarter, and more dangerous. Traditional security systems are no longer enough to protect data and systems.
This is where real-time threat monitoring plays a key role. It helps detect and respond to cyber attacks instantly, before they cause serious damage.
In this article by Tech Window, we will explore the real-time threat monitoring techniques used by experts to keep systems safe.
What Is Real-Time Threat Monitoring?
Real-time threat monitoring is the process of continuously tracking network activity to detect suspicious behavior.
Instead of reacting after an attack, this approach focuses on instant detection and response.
It helps in:
- Identifying threats early
- Preventing data breaches
- Protecting systems 24/7
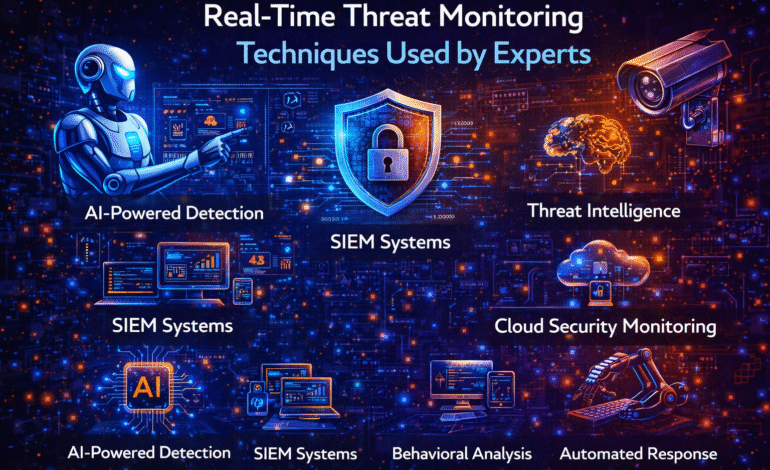
1. AI-Powered Threat Detection
Experts use Artificial Intelligence to monitor systems in real time.
AI tools such as ChatGPT and Google Gemini are part of a broader AI ecosystem that helps in analyzing large amounts of data quickly.
AI can:
- Detect unusual patterns
- Identify potential threats
- Learn from past attacks
This makes threat detection faster and more accurate.
2. Intrusion Detection Systems (IDS)
Intrusion Detection Systems are used to monitor network traffic.
They detect:
- Unauthorized access
- Suspicious activity
- Policy violations
IDS tools alert security teams when a potential threat is detected.
3. Security Information and Event Management (SIEM)
SIEM systems collect and analyze security data from multiple sources.
They provide a centralized view of security events.
SIEM helps in:
- Real-time analysis
- Threat detection
- Incident response
Experts rely on SIEM tools to manage large-scale security operations.
4. Behavioral Analysis
Behavioral analysis focuses on user activity.
Instead of just checking passwords, it analyzes behavior patterns.
For example:
- Login time
- Location
- Device usage
If something unusual happens, the system flags it as a potential threat.
5. Endpoint Monitoring
Endpoints include devices like laptops, smartphones, and servers.
Experts monitor these devices in real time to detect threats.
Endpoint monitoring helps:
- Detect malware
- Block unauthorized access
- Protect sensitive data
This is especially important for remote work environments.
6. Threat Intelligence Integration
Threat intelligence involves collecting data about known cyber threats.
Security systems use this data to identify and block attacks.
It includes:
- Known malware signatures
- Blacklisted IP addresses
- Attack patterns
This helps systems stay updated against the latest threats.
7. Automated Incident Response
Speed is critical in cyber security.
Experts use automated systems to respond instantly to threats.
Automation can:
- Block suspicious users
- Isolate infected systems
- Send alerts
This reduces damage and improves response time.
8. Network Traffic Analysis
Monitoring network traffic is a key technique.
It helps detect:
- Unusual data transfers
- Suspicious connections
- Data leaks
Experts analyze traffic patterns to identify threats early.
9. Cloud Security Monitoring
Many businesses use cloud platforms. This makes cloud security monitoring essential.
Experts track:
- User access
- Data movement
- Configuration changes
This helps prevent data breaches in cloud environments.
10. Continuous Security Updates
Cyber threats are constantly evolving.
Experts ensure that systems are always updated with the latest security patches.
Regular updates help:
- Fix vulnerabilities
- Improve system security
- Prevent new attacks
Related Topics You Should Explore
To understand cyber security better, also read:
👉 Top Cyber Security Threats in 2026 | Tech Window
👉 Best Cyber Security Tips to Stay Safe Online in 2026 | Tech Window
👉 Future of AI in Cyber Security and Online Safety | AI Security Guide
These topics will give you a complete understanding of online safety.
Final Thoughts
Real-time threat monitoring is essential in today’s digital world. It allows organizations to detect and respond to cyber threats instantly.
Techniques like AI monitoring, behavioral analysis, and automated response systems are helping experts stay ahead of attackers.
At Tech Window, we believe that understanding these techniques can help individuals and businesses improve their online security.
Staying informed and using modern security tools is the best way to stay protected in 2026.